Overview of PASERO's personal data handling
When visiting the website, PASERO-MI Ltd. collects Personal Data on its visitors and registered users. We don’t sell your Personal Data to anybody. Read this quick overview or go to the full privacy policy here:
Registration and billing
- To provision you the service- Personal data: name, email address, billing information
- Third Parties used: Amazon Web Services, ProtonMail, online payment&accounting service provider, accountant
- Retention: 8 years if required by law
Visitors and cookies
- For user experience & statistics- Personal data: IP, browser info, webpage usage information
- Third Parties used: Amazon Web Services, Google Analytics
- Retention: 90 days
Content
- Personal data you might upload when using the service- Personal data: contract signatories and contacts, name and email address of users, e-mail address of your customers, free text within comments and descriptions
- Third Parties used: Amazon Web Services
- Retention: until you have an account
Rights and questions
- Rights regarding Personal Data for Registered users
PASERO contact information
- if you have any questions- PASERO-MI Ltd.
- H-1221 Budapest, Ady Endre ut 87, Hungary
- privacy@pasero.me
How to be compliant with Schrems II in the cloud?
The judgement “Schrems II.” of the European Court of Justice was concluded on the 16 July 2020 (Case C-311/18, Data Protection Commissioner v Facebook Ireland Ltd, and Maximillian Schrems). The judgment contains the following main findings:
- The Compliance Decision allowing the transfer of data between the EU and the US, known as the Privacy Shield is invalid;
- Commission Decision 2010/87 on the general terms and conditions for the transfer of personal data to third country processors is valid. However, the Court has also laid down conditions for transfers based on general terms and conditions which must be examined before transfers to a third country in order to ensure adequate protection of personal data.
That decision of the CJEU requires data controllers to verify that the law of the third country ensures a level of protection of transferred personal data substantially equivalent to that guaranteed by the EEA. Data controllers are responsible for carrying out an assessment for the specific data transfer, the legislation of the third country and the means of transfer. However, data controllers should be aware that it is certainly possible that no additional measures will be sufficient for carrying out some data transfers.
While the EDPB did issue a guide on technical and organizational measures to help companies make international data transfers compliant, at first look these measures look inpractical for most cases and questions arise whether compliance can be achieved at all. A ruling in France in relation to the use of Amazon Web Services and Schrems II did provide reassurance that companies following good diligence and applying some particular controls don't need to be afraid of using the services of cloud providers.
In this article, we are going to summarise and illustrate with the examples of Amazon Web Services (AWS), Google Cloud Platform (GCP) and Microsoft Azure what these particular technical and organizational measure are and how to achieve them. We understand that the particular examples we are going to show cannot be applied to all kinds of cloud services, but they provide a good direction for measures to look for to be able to leverage the services of 3rd country providers.
Keep data and contracting within the EU
Cloud providers with headquarters in 3rd party countries could be instructed by law enforcement or other authorities to provide access to customer data in ways incompatible with GDPR. The very first step which provides huge reassurance to EU customers, is when the cloud provider hosts or has an option to host customer data exclusively within the EU or other recognized adequate country. While, on this own wouldn't necessarily mean that US authorities cannot request access, but the legal process is way more strict as if the data was sitting within a 3rd country. For example, after the Microsoft Corp v. United States case, the CLOUD act was introduced. The CLOUD act specifies the exact circumstances in which access to data can be requested by US authorities to data hosted outside the US, and these circumstances are stricter than requirements for access requests within the US. All of our selected example cloud providers have hosting locations within the EU.
For companies from 3rd party countries to credibly say that they cannot be instructed by public authorities of their country, they should have a legal entity within the EU, and European customers should be contracting with this entity. A European legal entity gives the customer reassurance that the cloud provider is subject to GDPR and will therefore ensure the rights and freedoms of the customer. For our 3 cloud providers, the respective European entities are Amazon Web Services EMEA Sarl, Google Ireland Limited, and Microsoft Ireland Operations Limited. For all customers with billing address within the EU, the cloud providers automatically use their European entities for contracting purposes.
There was a specific clause which the French court highlighted from the data processing agreement of the cloud provider. According this clause, the cloud provider should make a commitment to challenge access request from public authorities which are to broad or vague. Similar provisions are expected to be included with the upcoming reformed standard contractual clauses. The data processing agreements included in AWS's and Microsoft Azure's service agreements contain such provisions, while the respective whitepaper of GCP also references such challenges to happen.
Encryption as technical measure
The EDPB guidance on supplemental measures to protect personal data highlights the use of encryption as a technical measure. While only very few services can operate without having access to the actual data, the major public cloud service providers have sophisticated key management and encryption capabilities. The key vault services of these providers have options for both using customer managed keys or provider managed keys. The keys in the key vault can be used for encrypting customer data at rest and allow complete management and transparency into the use of the encryption keys. This way customers can achieve a great level of assurance that their data is protected from any access incompatible with the protections of GDPR.
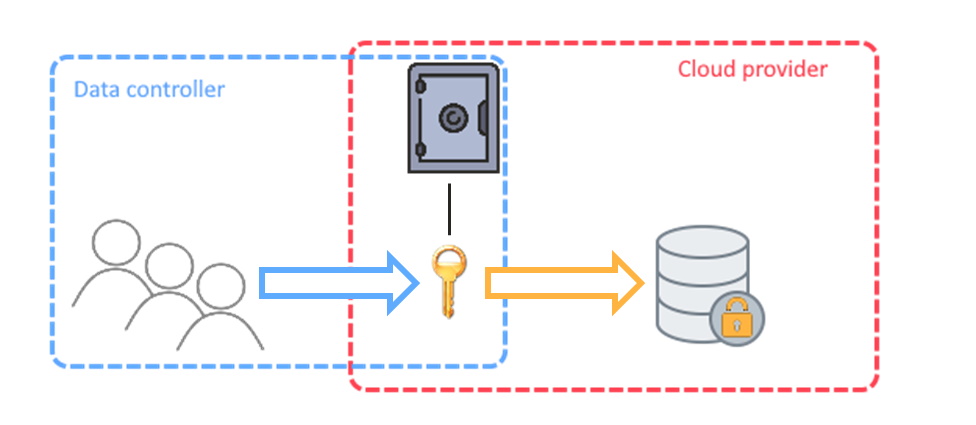
For storage encryption at rest, customers of Microsoft Azure and GCP should search for the option of customer managed keys in the Azure Key Vault and Cloud KMS respectively. For S3 encryption in Azure, the most convinient option which still provides the necessary protections is Server-Side Encryption with Customer Master Keys (CMKs) stored in AWS Key Management Service (SSE-KMS). All three of the cloud providers being looked at here have an option for customer-provided keys, meaning that the application has to provide the keys for decryption every time data is being accessed. While this significantly increases control over the data hosted in the cloud, the usability aspects and additional requirements of key management make this option mostly unfavourable.
Summary
Fortunately, with most of the mature cloud service providers, European customers can achieve compliance with the requirements of GDPR and the decision of the Schrems II case. Based on a recent ruling, companies only need to look out and implement some well achievable organizational and technical measures. Unfortunately, these measures are not available with all cloud service providers, but we strongly believe that cloud providers who wish to offer their services on the European market are soon going to adopt similar possibilities.
Get a demo!
Book a demo and let us show you, how we can take of the burden of managing your data processing agreements and help meet data protection regulatory compliance.


